In high-stakes environments – law enforcement agencies, military installations, and private security firms — managing lethal assets is a zero-error responsibility. Yet for decades, armories have depended on paper logs, spreadsheets, and legacy barcode systems to track firearms, magazines, and tactical equipment. The result? Slow processing, human error, and dangerous accountability gaps.
An RFID weapon tracking system eliminates these vulnerabilities entirely. By leveraging Radio Frequency Identification technology, organizations gain real-time, automated visibility over every asset in the armory – without requiring manual scans or line-of-sight alignment.
KEY INSIGHT
IoTWeaponTracker delivers enterprise-grade RFID weapon tracking systems purpose-built for organizations that cannot afford gaps in accountability.
What Is an RFID Weapon Tracking System?
An RFID weapon tracking system is an integrated hardware-software ecosystem that uses radio waves to automatically identify, monitor, and record the movement of weapons and tactical gear across a facility.
Unlike traditional barcodes — which must be individually scanned – RFID tags can be read in bulk from several feet away, with no line-of-sight required. When a tagged weapon passes through a monitored portal or is placed in a smart rack, the system instantly captures the asset’s unique ID, timestamp, and location. That data flows to a centralized management platform, creating an undisputed digital record of every movement.
This is not a digital clipboard. It is a fully automated chain-of-custody engine.
Core Components of an RFID Weapon Tracking System
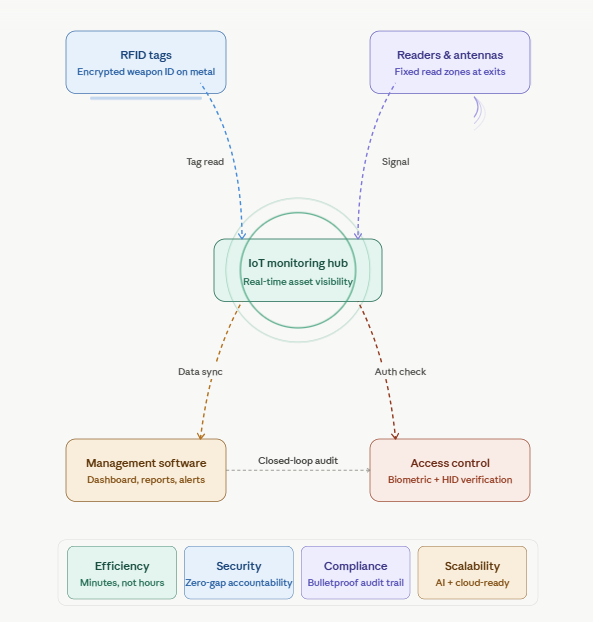
A high-performance RFID weapon tracking system relies on the seamless synchronization of four key components:
| RFID Tags | Low-profile transponders engineered to mount on metal surfaces without signal interference. Each tag stores encrypted data identifying the weapon’s make, model, and serial number. |
| Fixed Readers & Antennas | Strategically positioned at armory exits, exchange windows, and storage zones. These create automated read zones detecting every tagged asset entering or leaving — 24 hours a day. |
| Armory Management Software | The operational brain of the system. A centralized dashboard gives armorers complete visibility over inventory status, alert management, compliance reporting, and system health. |
| Access Control Integration | Connects with biometric scanners and HID card readers to verify user identity before authorizing any weapon release — eliminating unauthorized access at the point of issuance. |
RFID weapon tracking system – Architecture overview
Where are RFID readers and antennas typically installed in an armory?
RFID readers and antennas in an armory are strategically placed at every point where a weapon or asset transitions between zones or custody. Here’s where they’re typically installed:
Entry & Exit Points
- The main armory door or vault entrance — the most critical read zone, capturing every asset moving in or out
- Secondary access doors and emergency exits to prevent unauthorized removal going undetected
Exchange / Issue Windows
- The counter or window where weapons are formally signed out to personnel and returned after duty — this is where check-out and check-in transactions are recorded in real time
Internal Zone Transitions
- Doorways between the main vault and secondary rooms (cleaning room, maintenance bay, staging area) so the system always knows which zone a weapon is in, not just whether it’s “inside” or “outside”
Smart Racks and Storage Cabinets
- Some installations embed antennas directly into weapon racks or lockers, so the system knows the exact shelf position of each firearm — not just the room it’s in
Inspection / Audit Stations
- Desktop reader pads at an armorer’s workstation, used for quick individual scans during maintenance checks or serialization verification
Transit and Staging Areas
- Portals or handheld readers at loading docks or vehicle staging areas for deployments, ensuring weapons leaving the facility in transport cases are fully logged before they move
Key installation principles that guide placement: The exact layout is always determined by a professional site survey, since radio waves behave differently around dense metal racking, concrete walls, and reinforced doors. Antenna placement has to account for signal reflection and dead zones — which is why IoTWeaponTracker conducts a facility-specific RF mapping exercise before any hardware goes in. The goal is overlapping read zones with no gaps, so there is no physical path a tagged asset can travel without being detected.
How does the IoTWeaponTracker platform connect all parts of the RFID weapon tracking system?
What the hub actually is It’s not a single physical device — it’s a software layer (cloud or on-premise) that receives, processes, and distributes data streams from every connected component simultaneously. Think of it as a live switchboard that never sleeps.
How each component feeds into it
- RFID readers push raw tag-read events to the hub the moment a weapon enters a read zone — asset ID, antenna ID, timestamp, signal strength
- Access control systems send identity verification events — who authenticated, when, and at which door or window
- Environmental IoT sensors report cabinet door states, tamper alerts, temperature, and humidity in real time
- Handheld readers sync audit data wirelessly when armorers do roving inventory checks
What the hub does with that data Every incoming event is cross-referenced against the asset database and the last known state of that weapon. The hub is constantly asking: does this movement make sense? If a weapon appears at an exit reader but was never formally issued, the hub fires an alert and can trigger a door-lock signal back to the access control system — all within milliseconds, with no human in the loop.
The outbound side — what the hub pushes out
- Live dashboard updates to the armory management software
- SMS/email alerts to supervisors when anomalies occur
- Automatic log entries to the compliance audit trail
- Status updates to any integrated external systems (logistics platforms, HR systems for shift data, command-level dashboards)
Why the IoT architecture matters specifically Traditional systems were polling-based — a computer would ask “what’s changed?” on a schedule. IoT hubs are event-driven, meaning data flows the instant something happens. For a weapon tracking system, that difference between a 30-second polling lag and a sub-second alert can be the difference between catching an unauthorized removal in progress versus discovering it on the morning report.
The hub essentially collapses what used to be four separate siloed systems — inventory, access control, surveillance triggers, and compliance logging — into one unified event stream that any authorized stakeholder can query from anywhere.
What features does armory management software provide in an RFID weapon tracking system?
Armory management software is the operational brain that transforms raw RFID data into actionable intelligence. Here’s a comprehensive breakdown of what it provides:
Live Inventory Dashboard The centerpiece of the software is a real-time floor map showing the exact status and location of every asset — which weapons are in the vault, which are issued, which are in the cleaning room, and which are deployed in the field. No manual count needed at any point.
Weapon Check-Out and Check-In Workflow The software manages the complete issuance lifecycle. When a weapon is issued, it logs the officer’s verified identity, the specific asset, time of issue, and authorized duration. When returned, it closes the transaction and flags any overdue returns automatically. The entire process that once required paper forms now takes seconds.
Automated Audit Trails and Compliance Reporting Every single movement is permanently archived with full chain-of-custody detail — who had what weapon, for how long, and where it went. These logs can be exported on demand for regulatory inspections, internal investigations, or legal proceedings. Because the records are machine-generated, they are tamper-resistant in a way paper logs never can be.
Alert and Notification Engine The software monitors for anomalies continuously and pushes alerts to supervisors when something falls outside authorized parameters, including:
- Weapons not returned by end of shift
- Assets detected near an exit without a valid issuance record
- Cabinet access outside authorized hours
- Tamper events on secure storage units
Maintenance Scheduling and Equipment Health Each weapon has a digital profile tracking its service history, round counts, and inspection dates. The software automatically generates maintenance reminders and flags weapons that are due for inspection before they can be issued — ensuring nothing deploys in substandard condition.
User and Role Management Administrators can define exactly which personnel have access to which weapons, at which times, and under what authorization levels. Two-person rules for heavy weaponry, rank-based access tiers, and time-restricted permissions are all configurable without touching the hardware.
Multi-Site Command View For organizations managing multiple armories across cities, states, or countries, the software aggregates data from all locations into a single command dashboard. A regional commander can see total equipment readiness across every facility without making a single phone call.
Analytics and Reporting Beyond compliance, the software generates operational intelligence — usage patterns by weapon type, issue frequency by unit, peak demand periods, and maintenance cost trends. This data informs procurement decisions, staffing, and long-term equipment planning.
Integration APIs Enterprise-grade armory software connects outward to HR systems for shift and personnel data, logistics platforms for deployment tracking, and surveillance systems for correlated video bookmarking. The software doesn’t operate in isolation — it becomes a node in the organization’s broader security infrastructure.
The practical result is that an armorer who previously spent hours on manual counts and paperwork can now manage a larger, more complex inventory with greater accuracy in a fraction of the time — with a complete, defensible record of everything that happened on every shift.
How does access control integration prevent unauthorized weapon removal?
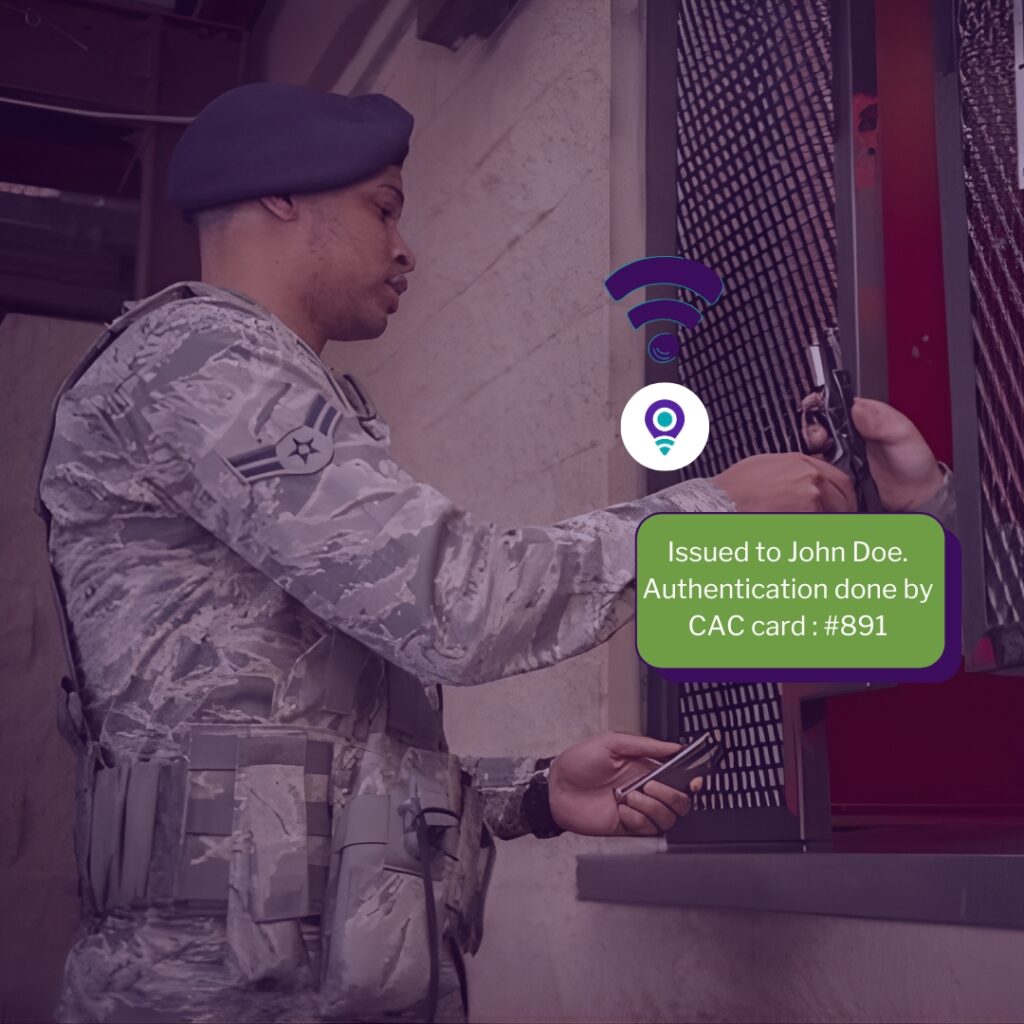

Access control integration is what gives the RFID weapon tracking system its enforcement teeth – it’s the difference between a system that records what happened and one that actively prevents the wrong thing from happening. Here’s exactly how it works:
The Core Principle: Dual Verification No weapon can leave the armory unless two independent conditions are satisfied simultaneously — the person’s identity is verified, and that person is authorized to take that specific weapon at that specific time. If either condition fails, the system blocks the transaction before the weapon ever leaves the rack.
How Identity Verification Works The system supports multiple authentication methods, and organizations typically layer them:
- HID card readers — personnel swipe or tap an encrypted proximity card
- Biometric scanners — fingerprint, retinal, or palm readers confirm physical identity that cannot be borrowed or shared
- PIN codes — a secondary factor added on top of card or biometric for sensitive weapons or high-security zones
- Two-person authorization — for heavy weaponry or restricted assets, the system requires two separately verified personnel to authenticate before the locker releases
The Real-Time Authorization Check When someone authenticates at an exchange window or smart locker, the access control system instantly queries the armory management software against several parameters:
- Is this person currently on an active, authorized shift?
- Do they hold the rank or clearance required for this weapon class?
- Has this weapon been formally flagged for issuance to this person?
- Is the current time within their authorized access window?
If every check passes, the transaction proceeds. If any check fails, the locker stays locked and a supervisor alert fires immediately.
What Happens at the Physical Exit RFID readers at every egress point create a final enforcement layer. If a tagged weapon approaches an exit and the armory management software has no matching open issuance record for it, the system can:
- Trigger an audible alarm at the armory station
- Send an immediate push alert to the duty supervisor’s device
- Electronically lock the facility door via the building’s PACS integration
- Automatically bookmark the surveillance camera feed at that exact timestamp
This happens in under a second — faster than a person can walk through a door.
Preventing Internal Threats Specifically Most unauthorized removal scenarios involve insiders — personnel who have legitimate access to the building but are attempting to take a weapon outside their authorization. The integration is specifically designed to close these gaps:
- A valid building access card does not grant armory access
- Armory access does not automatically authorize weapon removal
- Weapon removal authorization is asset-specific, not class-wide — being cleared for a sidearm does not authorize removal of a rifle
- Every failed authentication attempt is logged with identity, timestamp, and location, creating an evidence trail even when the attempt is unsuccessful
After the Weapon Leaves: Continuous Accountability Access control integration doesn’t end at the door. The issued weapon remains linked to the verified individual in the system. If it isn’t returned by the end of the authorized period, the software escalates alerts through the chain of command automatically — no manual follow-up required from the armorer.
The Net Effect: What access control integration ultimately creates is a closed loop with no gaps. Every point at which a weapon could leave authorized custody — the storage rack, the exchange window, the facility exit — has a verified identity gate in front of it. The system doesn’t rely on human vigilance at any single point, which means it works consistently at 3am on a holiday just as reliably as it does during a busy shift change.
System Integration: Building a Unified Security Ecosystem
The greatest competitive advantage of a modern RFID weapon tracking system is its ability to integrate with existing security infrastructure — turning isolated tools into a unified, intelligent platform.
Integration with Physical Access Control Systems (PACS)
When a weapon moves toward an exit without being properly issued in the software, the system can automatically lock electronic doors and bookmark the surveillance feed — no human intervention required. This creates a continuously active security layer that legacy systems simply cannot replicate.
Integration with Inventory and Database Platforms
IoTWeaponTracker’s RFID weapon tracking system connects directly to an organization’s master inventory database, updating asset status in real time. Regional commanders and logistics officers can view equipment readiness across multiple facilities from a single command center.
IoT-Enabled Real-Time Monitoring
Modern weapon tracking has evolved far beyond static inventory counts. Today’s systems leverage IoT sensors to deliver:
- Real-time asset visibility — a live digital floor plan showing exactly where every weapon is located, from the vault to the field
- Automated audit trails — a complete chain of custody for every asset, logging each transaction with time, date, and verified user identity
Tamper detection alerts — immediate notifications to leadership if a secure cabinet is accessed outside authorized hours or if a device is forcibly removed
How to Implement an RFID Weapon Tracking System: Step-by-Step
Phase 1: Infrastructure Planning and Site Survey
Every facility is unique. Radio waves interact differently with metal racks, concrete walls, and open floor plans. IoTWeaponTracker consultants conduct a comprehensive site survey to determine optimal antenna placement and map existing workflows — identifying bottlenecks the new system will resolve.
Phase 2: Asset Tagging and Digital Registration
Every weapon, magazine, and serialized piece of gear is outfitted with an RFID tag and matched to its digital twin in the database. Because RFID enables bulk scanning, a full inventory count that once took days now takes minutes. Maintenance schedules and expiration alerts are configured during this phase.
Phase 3: Hardware Installation and Software Configuration
Tracking portals, desktop scanning stations, and smart lockers are installed and calibrated. The software is then configured to mirror the agency’s specific protocols — including two-person authorization rules for heavy weaponry and digital signature requirements at the point of issuance.
Phase 4: Staff Training and Operational Adoption
Technology only delivers value when personnel use it correctly. Training sessions cover handheld RFID reader operation for rapid field audits, dashboard alert interpretation, and the complete digital issuance workflow. IoTWeaponTracker ensures the transition from manual logs to a fully digital system is professionally managed from day one.
Key Benefits of Deploying an RFID Weapon Tracking System
The shift toward an integrated RFID environment yields immediate returns in terms of safety, cost savings, and organizational accountability.
| Benefit | Description |
| Operational Efficiency | Full inventory count in minutes instead of hours. Armorers use a handheld reader or dashboard for instant 100% accurate results. |
| Enhanced Security | Closed-loop tracking ties every weapon to a verified user and location. Anomalies trigger automatic supervisor alerts in real time. |
| Compliance & Audit Trails | Automated logs create bulletproof, tamper-proof records satisfying federal, state, and military regulatory requirements. |
| Scalability | Platform grows with the organization — supporting AI analytics, predictive maintenance, and cloud-based multi-site command centers. |
Frequently Asked Questions
Yes. IoTWeaponTracker uses ruggedized, low-profile tags engineered specifically for metal-surface mounting, making them compatible with handguns, rifles, shotguns, and heavy weapons systems.
By integrating with biometric and card-based access control systems, the RFID weapon tracking system creates a dual-verification checkpoint: a weapon cannot be released unless the user’s identity is confirmed and the issuance is logged in the software.
Absolutely. The cloud-based architecture allows administrators to monitor inventory and compliance across multiple facilities simultaneously from a centralized dashboard.
Conclusion
Implementing an RFID weapon tracking system is one of the most impactful operational investments a security-focused organization can make. By replacing manual processes with automated, IoT-integrated tracking, agencies achieve a level of visibility, accountability, and compliance that legacy methods cannot approach.
IoTWeaponTracker provides the hardware, software, and implementation expertise to transform your armory into an intelligent, data-driven security hub. Every firearm accounted for. Every transaction recorded. Every compliance requirement met – automatically.